Amazon. com Help About Multi-Factor Authentication
 Sicherer Zugriff auf Windows/Mac und Verschlüsselung mit USB-Stick
Sicherer Zugriff auf Windows/Mac und Verschlüsselung mit USB-Stick
Rohos Logon Key v3.9 provides an effective and platform independent means of Multi-factor Authentication for your Amazon WorkSpaces desktops. You can protect access to AWS Windows desktops with Google Authentication OTP codes or Yubikey OTP codes. This greatly increase security, brings compliance with HIPPA, PCI-DSS or works as a password replacement technology.
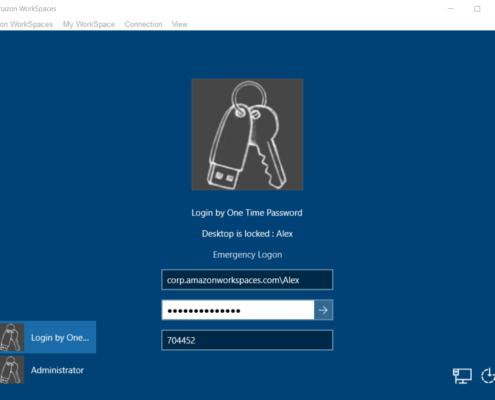
Amazon WorkSpaces is a managed and secure Windows desktop service in AWS cloud. You can provision Windows 10 or Windows Terminal Servers in just a few minutes and quickly scale to provide multiple of desktops to workers across the globe. By default access is protected by two step authentication: AWS password and Windows password.
How to setup strong two-factor authentication control for WorkSpaces computer
1. Install Rohos Logon Key on a cloud Windows:
Open Rohos Logon Key – Click Options > More…
Copy/Paste this value:
Into “Disabled Cred Prov.” field as shown in the screenshot below. Click OK.

The value represents the Amazon provided authentication component pcoip_credential_provider. dll which is pre-installed on a cloud Windows. This authentication component implements a pass-through single factor password based authentication into Windows hosted by AWS CloudSpaces. It receives Windows password from Amazon WorkSpaces application and pass it to Windows logon screen.
In Order to prevent Single Factor authentication Rohos needs to filter-out it from logon screen.
Also in Options you need to select “For listed users” option.

Now strong MFA controls is enabled and you can continue to setup additional Authentication factors: Google Authenticator or Yubkey device.
How to setup Google Authenticator or Yubikey OTP for WorkSpaces
To setup Google Authenticator:
Open Rohos Logon Key > Setup OTP. choose desired user account and select Google Authenticator. Click on display QR code – to scan configuration code with Google Authenticator application installed in your smartphone. Click Enable OTP login. Done!

To setup Yubikey in default 44 bytes OTP mode:
Open Rohos Logon Key > Setup authentication device. Choose Yubikey device type. Click Gear to open Yubikey options and check “Verify OTP on yubico servers”. Optionally you may enter user Windows password – to enable password replacement method. Click Setup The Key. Done!

Rohos Logon Key licensing is lifetime (perpetual), price is one time payment. You can use the product forever. Minor updates are free (3.*) . Major updates are optional and cost 40% from the original license price. A Windows hosted in AWS WorkSpaces considered as a computer and require a separate license each. If you host Windows Server version then you need Rohos Logon Key Server license. Support by email is always free.
About Rohos Logon Key software
 Rohos replaces password based Windows login with a security key or adds strong two-factor authentication policy. Multi-factor Authentication decision framework allows to combine Passwords, PIN codes, Smartphones as well as strong authentication devices like U2F FIDO keys, Yubikey, Google Authenticator one-time codes, SafeNet iKey tokens or RFID cards. With Rohos you can protect standalone computers, Terminal Servers remote desktop and Active Directory workstations as well.
Rohos replaces password based Windows login with a security key or adds strong two-factor authentication policy. Multi-factor Authentication decision framework allows to combine Passwords, PIN codes, Smartphones as well as strong authentication devices like U2F FIDO keys, Yubikey, Google Authenticator one-time codes, SafeNet iKey tokens or RFID cards. With Rohos you can protect standalone computers, Terminal Servers remote desktop and Active Directory workstations as well.
Amazon AWS – Understanding IAM – Multi-Factor Authentication
VMware Boot Camp
Earn 3 certs in our 7 day class!
Practice for certification success with the Skillset library of over 100,000 practice test questions. We analyze your responses and can determine when you are ready to sit for the test.
This article will discuss the Multi-Factor Authentication (MFA) in AWS Identity and Access Management(IAM) .
The times when only a username and a password are needed to protect your email account or any other type of access to different resources are gone. Even if you are using a strong password, it’s just a matter of time until someone will break it. In the recent history, there have been several occasions when unauthorized people stole millions of usernames and passwords from different companies.
VMware Training – Resources (Intense)
Obviously it’s not enough having your accounts being protected only by passwords. Amazon is taking one step further and provides MFA.
MFA provides an additional layer of security for the AWS root account or for any other IAM user. Once MFA is configured, whenever a user will login to AWS, he/she will have to enter a unique code from the authentication device.
To configure MFA, you must link a MFA device (it can be hardware or virtual) to the root account or IAM user. The MFA device must be unique per user (regardless of its root account or IAM user).
There are three major steps in setting up and using the MFA device:
- Procure the MFA device – the device can be hardware or virtual. Virtual means that the device can be any device on which you can install a time-based one time password application. A virtual device is commonly a smartphone. Amazon maintains a list with the applications that can be installed on virtual devices based on the OS (Android, iOS, Windows). The hardware device is a Gemalto brand that is supported by AWS. Enable the MFA device – link the MFA device with your account. Use the MFA device – each time you access AWS, you will be asked for a username, password and a MFA code
In this article we will set up MFA for an IAM user. A user, user_01, has been created as you can see below:
Below on the same page, you can check if MFA is enabled for this user. In this case, it isn’t.
Let’s start the process to enable MFA for this user.
From the users list, select the user for which you want to enable MFA. Then open “Security Credentials” section and click on “Manage MFA Device” . On the pop-up window, select “A virtual MFA device” and click on “Next Step”:
You will be reminded that you need to install the application to a smartphone or PC. If you already d >“Next Step”:
Once you do that, you will be shown a QR code that you need to scan using the virtual device. If the virtual device does not support scanning, you can copy and paste the secret configuration key to the application. The application will generate random authentication codes. You will need to fill in two consecutive codes and then click on “Next Step”:
If everything was in order, the next window will tell you that the MFA device was successfully associated with the IAM user:
You might remember from the article Amazon Web Services: Understanding IAM – Users, Groups and Sign-in Credentials (http://resources. intenseschool. com/amazon-aws-understanding-iam-users-groups-and-sign-in-credentials/) that when a user wants to login to AWS, he/she has to use the following link: https://.signin. aws. amazon. com/console.
So let’s try to login with this user, but without using the MFA code. You will see that although the username/password combination is fine, you will be informed that the credentials are not correct:
Now let’s try one more time using MFA code as well:
As you can see, the authentication was successful:
It’s possible that sometimes the MFA device gets out of synchronization. If this happens then that user will not be able to login anymore in AWS. That user will be prompted to resynchronize the MFA device using the same procedure (the user will have to insert two consecutive codes). However, the synchronization can be done through the AWS Management Console. On an IAM console, select “Users” and then select the user for which you want to do the synchronization. Open the “Security Credentials” section and click on “Manage MFA device”:
Then you will be asked for two consecutive codes.
To deactivate the MFA for a user, follow the same steps as when you are synchronizing the MFA device, but now select “Deactivate MFA device” and click on “Next Step”. The device will be deactivated without any further actions.
MFA can be activated for the root account as well. Open the IAM console and on the dashboard, you will see “Activate MFA on your root account”. Click on “Manage MFA” and repeat the same procedure as you would activate MFA for a regular user:
So what happens if your virtual/hardware device stops working or it’s lost or stolen?
If that happens and you were using MFA for a regular user, then you need to contact the person who provided you the username and password for the account. He/she will have to deactivate the MFA device.
On the other hand, if that was the MFA device used for the root account, then you need to contact AWS Support and ask to disable temporary MFA so that you could access the AWS resource using only the username/password combination. Once you have a new hardware or virtual device, you can enable back MFA.
It’s recommended that you enable MFA not only for AWS access, but wherever it’s possible. It’s providing increased security. Passwords can be stolen at any time; someone might see what you are typing and so on. If you add MFA level of protection, the odds that someone gains unauthorized access to your AWS account are very low.
Krebs on Security
In-depth security news and investigation
How to Enable Multifactor Security on Amazon
Amazon has added multi-factor authentication to help customers better secure their accounts from hackers. With this new feature enabled, thieves would have to know your username, password, and have access to your mobile device or impersonate you to your mobile provider in order to hijack your Amazon account. The security feature allows users to receive a one-time code via text message, automated phone call, or third-party app — such as Google Authenticator.
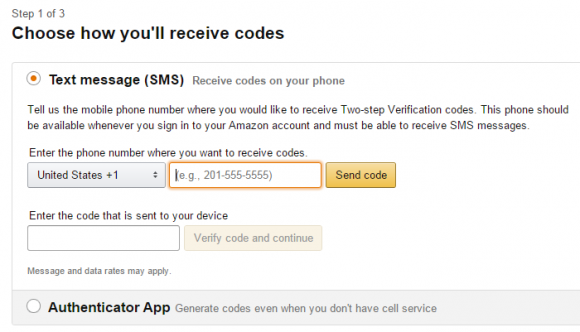
Step one of enabling multi-factor identification on your Amazon account.
Multi-factor authentication, also often called “two-step” or “two factor” authentication, is a great way to improve the security of your various online accounts (where available). With multi-factor logins enabled, even if thieves somehow steal your account username and password they’ll still need access to the second factor — your mobile phone — to successfully hijack your account.
Users can instruct Amazon to “remember” each device, which disables future prompts for the second factor on that device going forward. If Amazon later detects a login attempt from a device it does not recognize as associated with that account, it will prompt for the code from the second factor — text message, voice call, or app (whichever you choose).
I’m not sure I succeeded the first time I tried to set up multi-factor authentication on Amazon. I signed in, clicked “Your Account,” and then under “Account Settings” clicked “Change Account Settings.” That page allowed me to add a mobile number by typing in a code that was sent to my mobile. But when I hit “Done” and went back to Amazon’s home page, I decided to revisit the page only to discover that there are two more steps needed to finish setting up multi-factor authentication.
In step two, Amazon asks for a backup phone number where users can receive text messages or voice calls, in case you don’t have access to the mobile device added in Step 1. The backup method also can be Google’s Authenticator App.
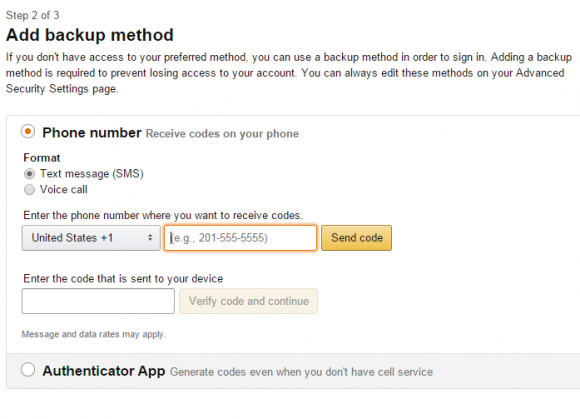
Step two of three for enabling multi-factor authentication on Amazon.
Step three just explains how it all works and allows users to skip future one-time codes on personal devices.
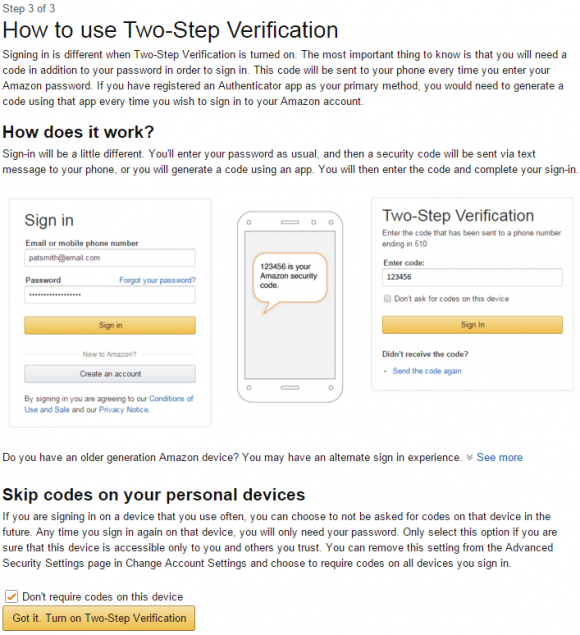
If you shop at Amazon, take a few minutes today to turn on multi-factor authentication for your account. While you’re at it, check out twofactorauth. org to see if multi-factor is available for other any online services you may use. Also, consider whether you’re able to beef up the security of the backup email accounts you use for your recovery address.
One final note: Receiving one-time codes by a third-party mobile app that does not require a working connection to the Internet — such as Google Authenticator — allows for fewer chances that your one-time codes could be diverted by attackers: Thieves can still call in to your Internet service provider or mobile provider, pretend to be you, and have your calls and/or texts forwarded to another number that they control.

This entry was posted on Monday, November 23rd, 2015 at 11:16 am and is filed under Security Tools. You can follow any comments to this entry through the RSS 2.0 feed. Both comments and pings are currently closed.
59 comments
Sadly two-factor doesn’t seem to be available on amazon. co. uk. It’s not mentioned in the help and all the google searches which reference it take you to amazon. com. 🙁
It is available, but not directly on the uk website – I had to go to amazon. com and set it up there first, but once I’d set it up, it had also taken effect on amazon. co. uk
I turned on Amazon 2-factor using Google Authenticator and it seemed to work fine everywhere except the Kindle app on my android. (Worked fine for the Amazon music app on the same device.) Tried several times on the Kindle app, resetting the password, etc., but no go. Once I disabled 2-factor I was able to get into the app straight away.
Using Multi-Factor Authentication (MFA) in AWS
For increased security, we recommend that you configure multi-factor authentication (MFA) to help protect your AWS resources. You can enable MFA for IAM users or the AWS account root user. When you enable MFA for the root user, it affects only the root user credentials. IAM users in the account are distinct identities with their own credentials, and each identity has its own MFA configuration.
Topics
What Is MFA?
MFA adds extra security because it requires users to provide unique authentication from an AWS supported MFA mechanism in addition to their regular sign-in credentials when they access AWS websites or services:
Virtual MFA devices. A software app that runs on a phone or other device and emulates a physical device. The device generates a six-digit numeric code based upon a time-synchronized one-time password algorithm. The user must type a valid code from the device on a second webpage during sign-in. Each virtual MFA device assigned to a user must be unique. A user cannot type a code from another user's virtual MFA device to authenticate. Because they can run on unsecured mobile devices, virtual MFA might not provide the same level of security as U2F devices or hardware MFA devices. We do recommend that you use a virtual MFA device while waiting for hardware purchase approval or while you wait for your hardware to arrive. For a list of a few supported apps that you can use as virtual MFA devices, see Multi-Factor Authentication. For instructions on setting up a virtual MFA device with AWS, see Enabling a Virtual Multi-factor Authentication (MFA) Device (Console).
U2F security key. A device that you plug into a USB port on your computer. U2F is an open authentication standard hosted by the FIDO Alliance. When you enable a U2F security key, you sign in by entering your credentials and then tapping the device instead of manually entering a code. For information on supported AWS U2F security keys, see Multi-Factor Authentication. For instructions on setting up a U2F security key with AWS, see Enabling a U2F Security Key (Console).
Hardware MFA device. A hardware device that generates a six-digit numeric code based upon a time-synchronized one-time password algorithm. The user must type a valid code from the device on a second webpage during sign-in. Each MFA device assigned to a user must be unique. A user cannot type a code from another user's device to be authenticated. For information on supported hardware MFA devices, see Multi-Factor Authentication. For instructions on setting up a hardware MFA device with AWS, see Enabling a Hardware MFA Device (Console).
SMS text message-based MFA. A type of MFA in which the IAM user settings include the phone number of the user's SMS-compatible mobile device. When the user signs in, AWS sends a six-digit numeric code by SMS text message to the user's mobile device. The user is required to type that code on a second webpage during sign-in. Note that SMS-based MFA is available only for IAM users. You cannot use this type of MFA with the AWS account root user. For more information about enabling SMS text messaging-based MFA, see PREVIEW – Enabling SMS Text Message MFA Devices.
AWS will soon end support for SMS multi-factor authentication (MFA). We are not allowing new customers to preview this feature. We recommend that existing customers switch to one of the following alternative methods of MFA: virtual (software-based) MFA device, U2F security key, or hardware MFA device. You can view users in your account with an assigned SMS MFA device. To do so, go to the IAM console, choose Users from the navigation pane, and look for users with SMS in the MFA column of the table.
For answers to commonly asked questions about AWS MFA, go to the AWS Multi-Factor Authentication FAQs.


Комментариев нет